Creating a marketing portfolio: tips and examples
Jul 05, 2024

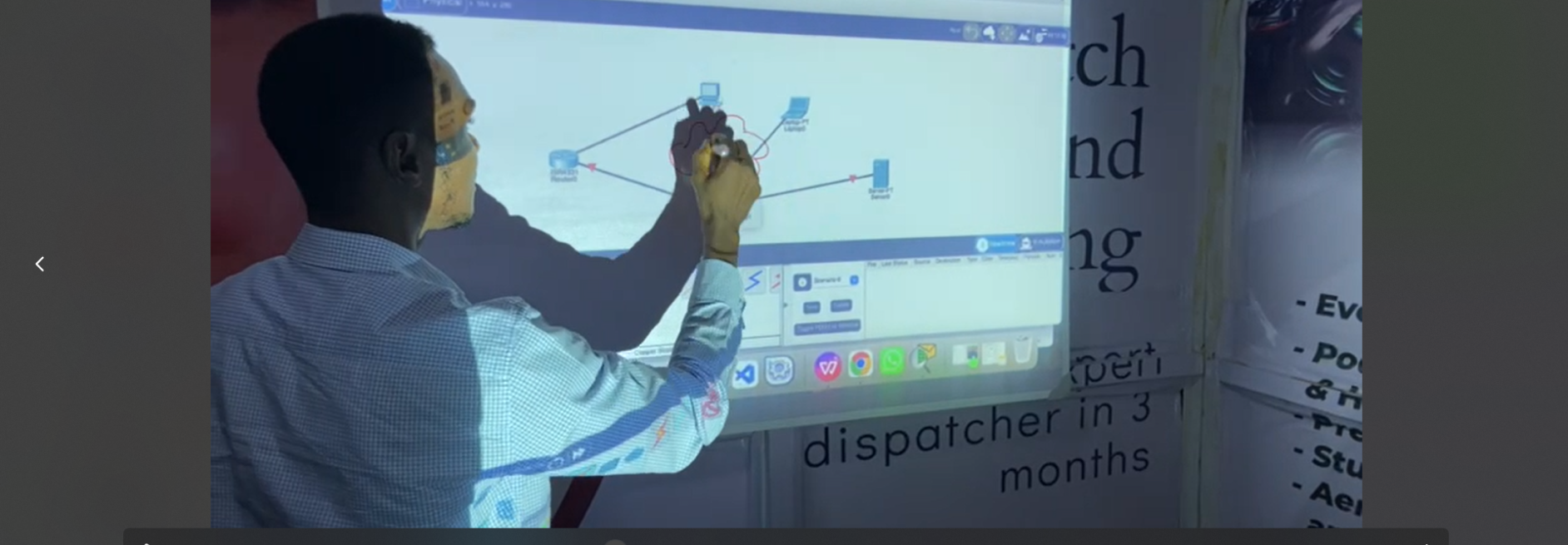
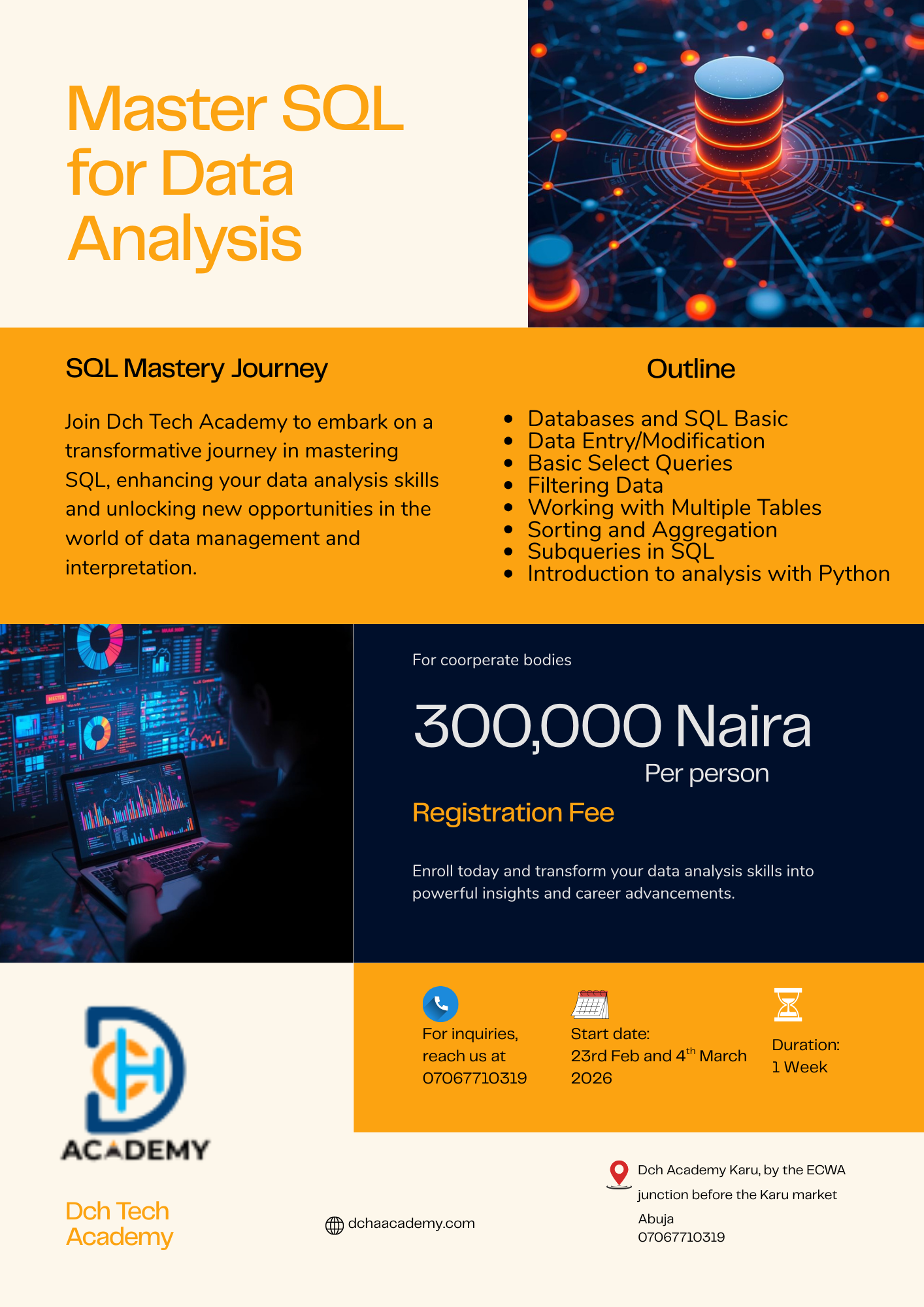
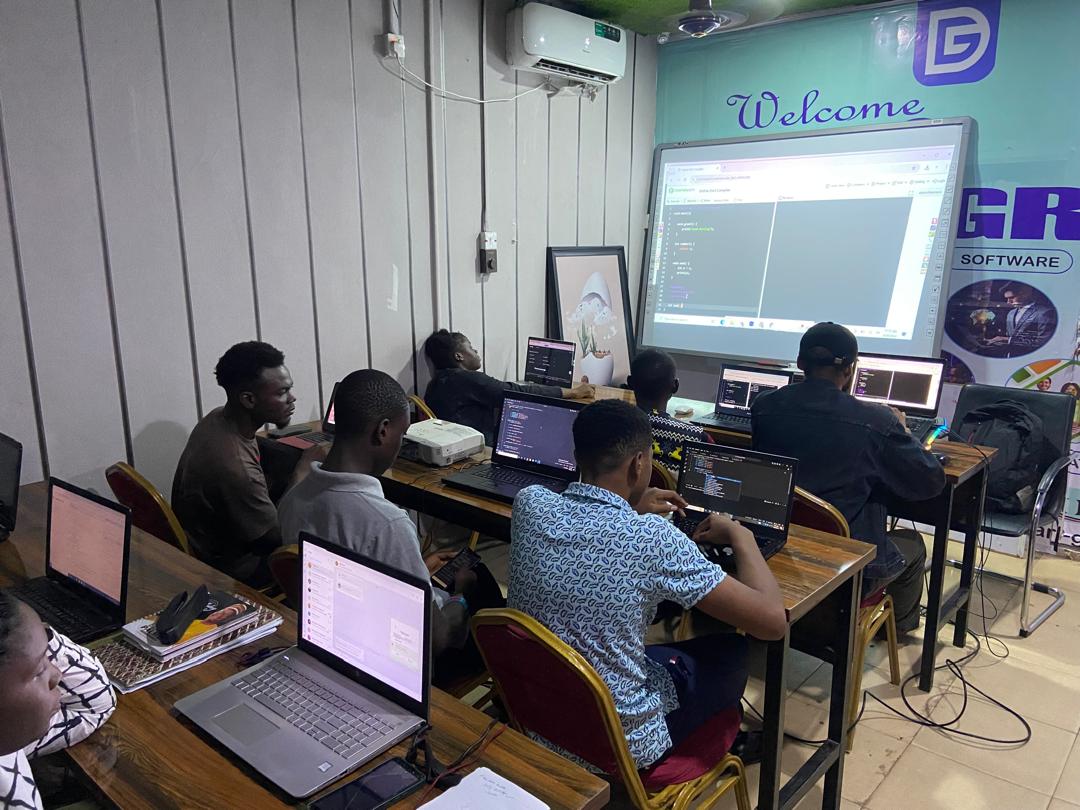
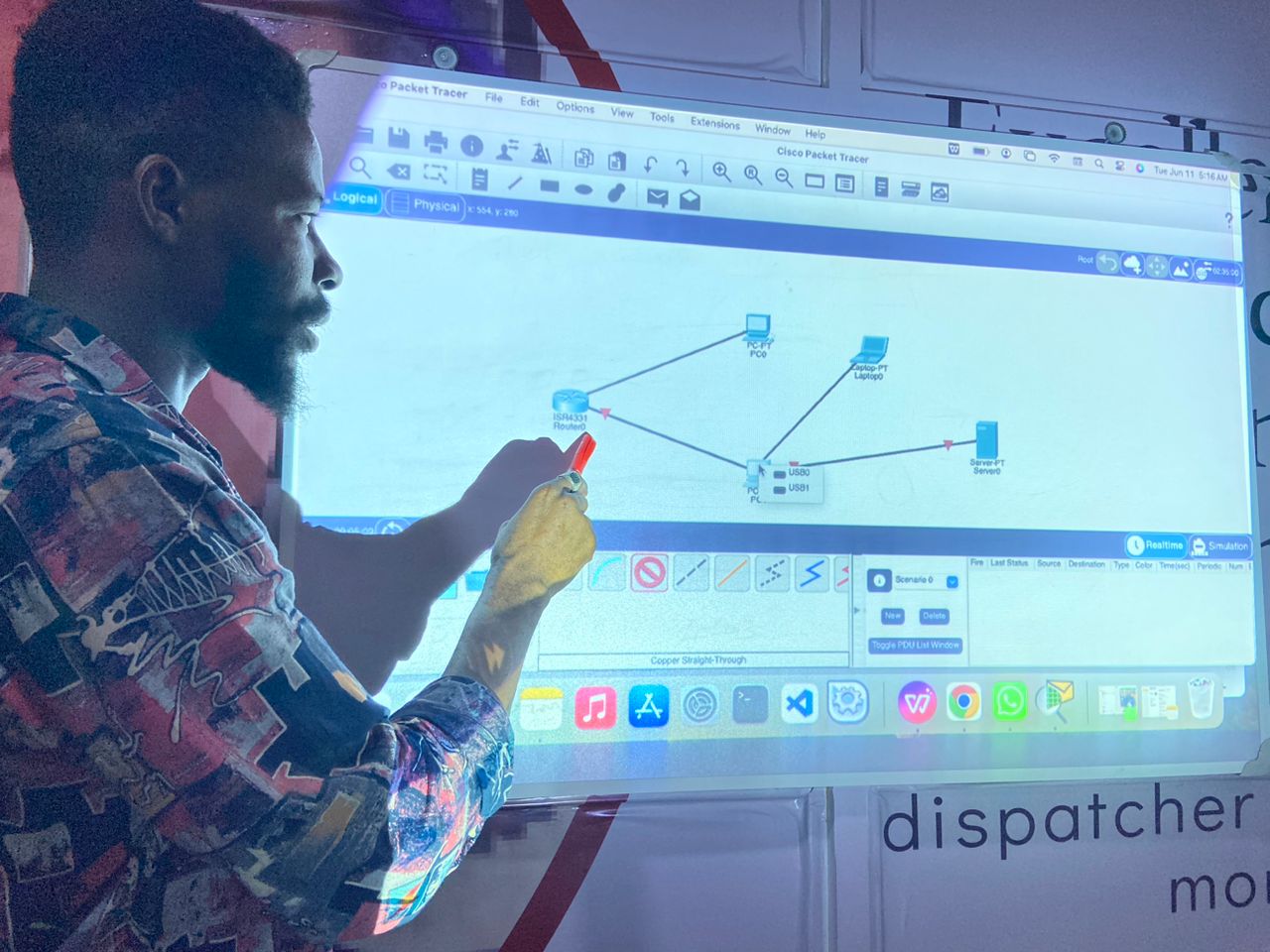
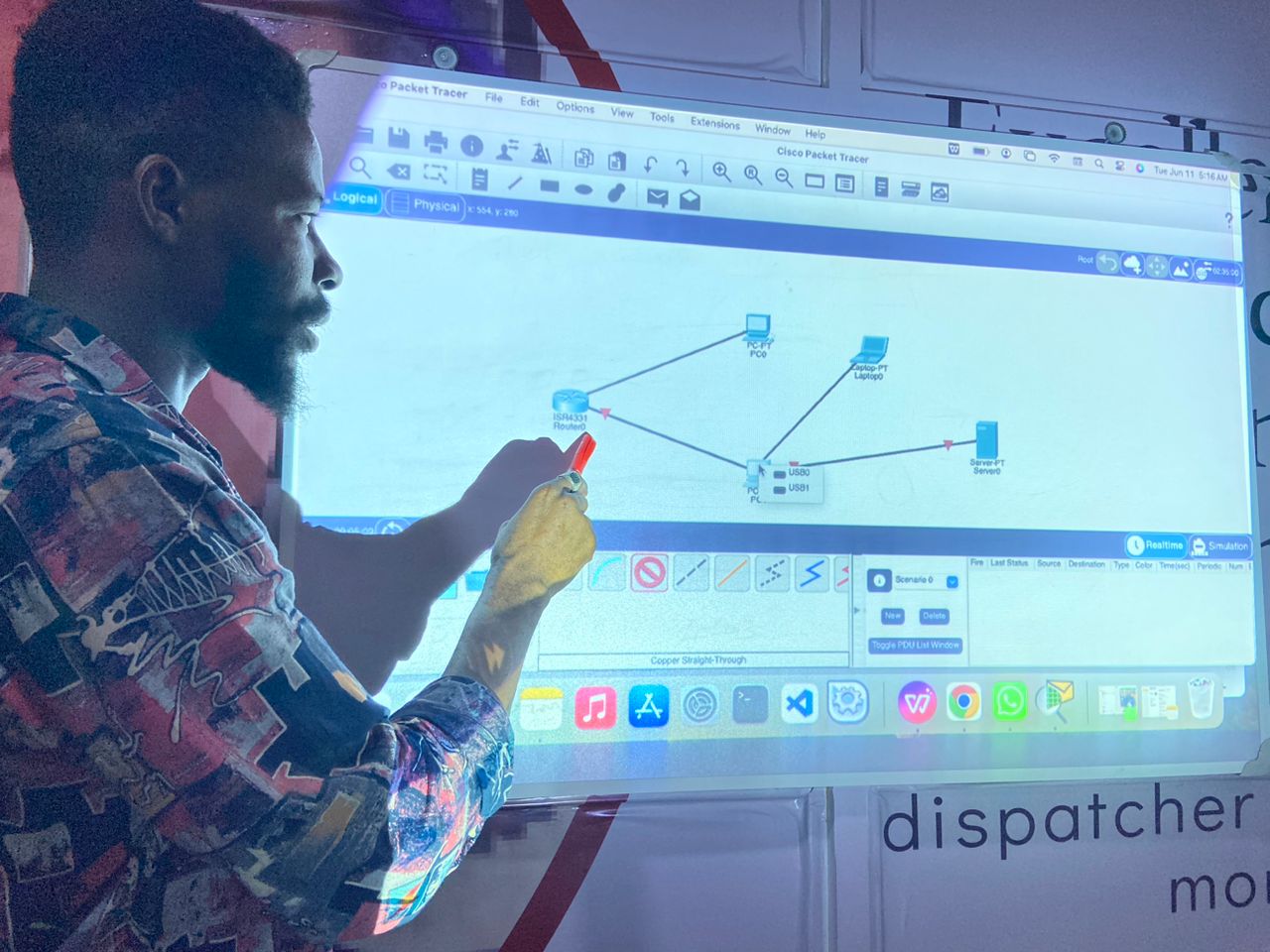
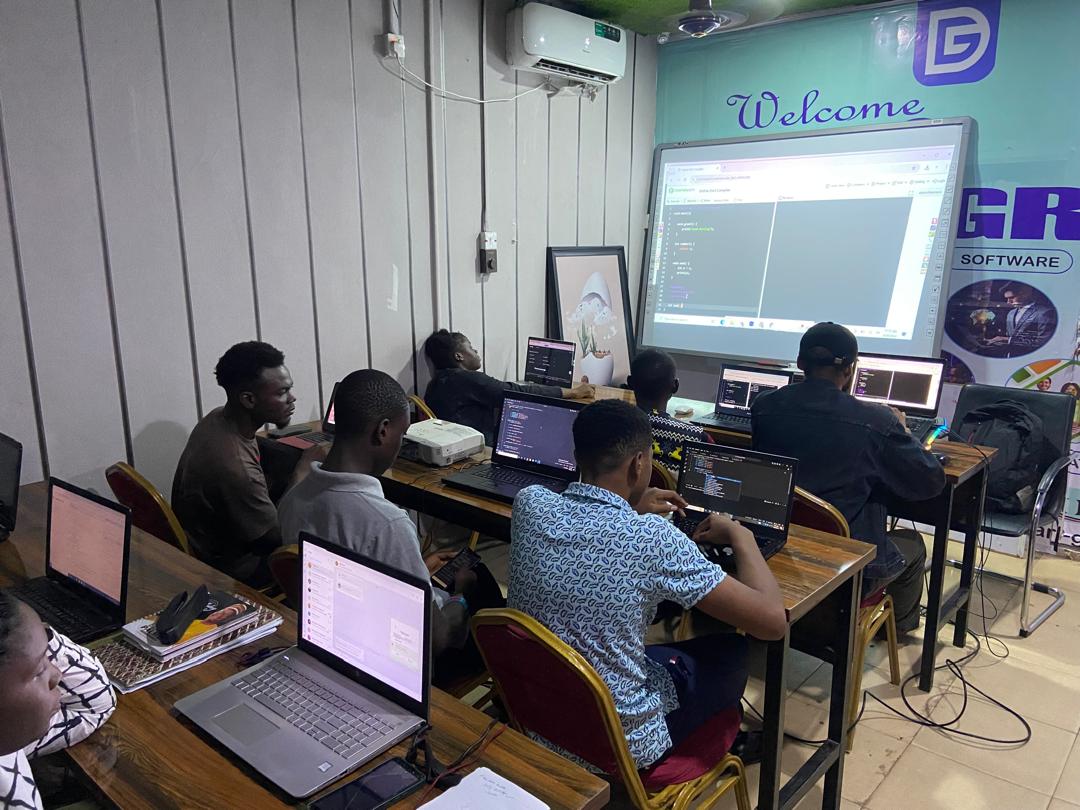
In this Ethical Hacking and Cybersecurity Training in Karu, Abuja, you'll learn to identify system or network weaknesses to exploit security vulnerabilities and gain access to sensitive data. You'll understand password-cracking algorithms and how to breach computer systems. Additionally, you'll discover how networking with external businesses exposes systems to hackers and how cybercrimes cost organizations millions annually.
You'll explore Footprinting and Reconnaissance techniques to gather information about target systems or networks. Learn about Passive and Active Footprinting, and understand why gathering extensive information is crucial for hackers to plan effective attacks.
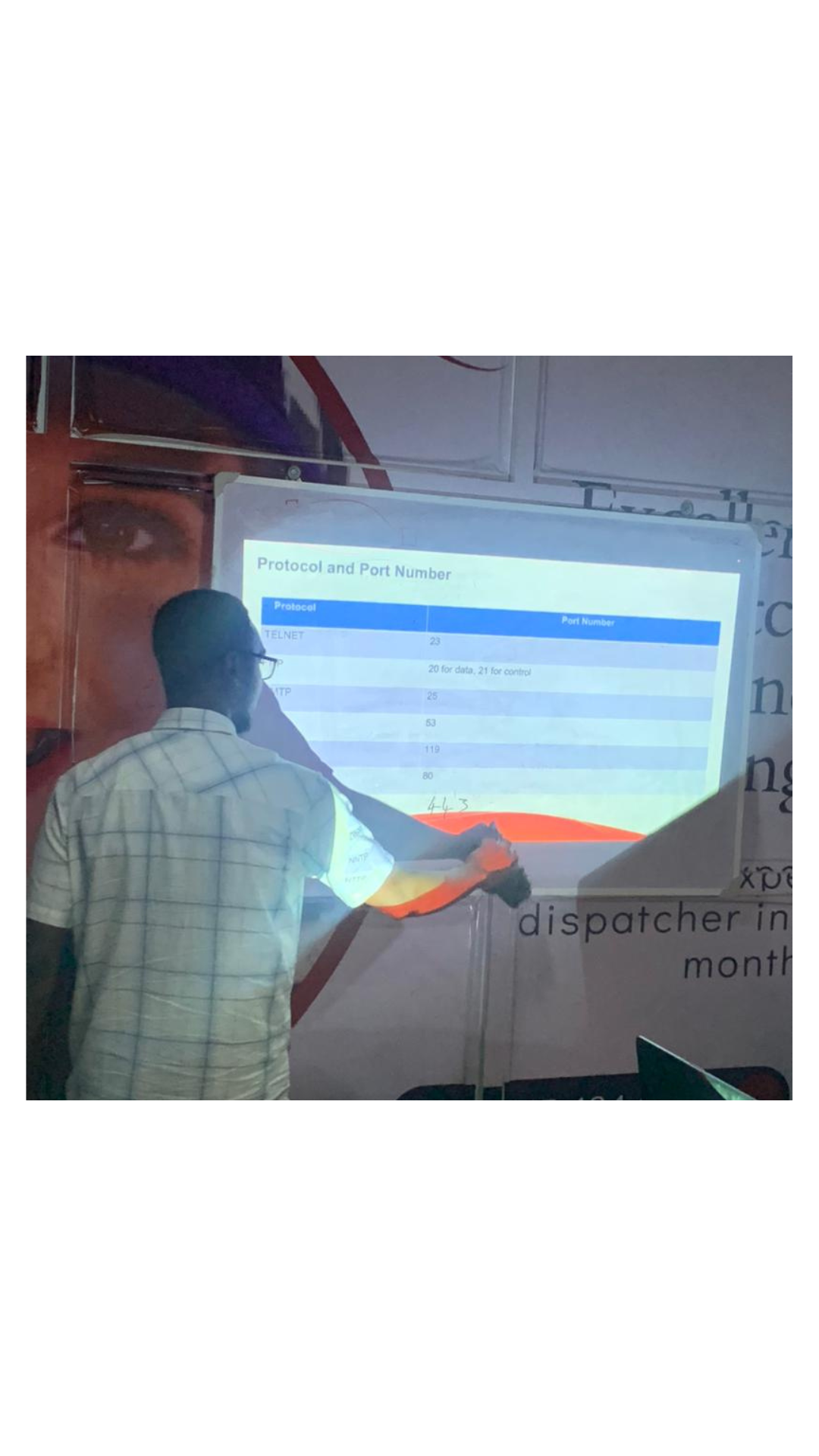
In this ICT training course in Karu, Abuja, you'll grasp the significance of network scanning in managing, maintaining, and securing systems. Discover how network scanning identifies services, recognizes filtering systems, examines operating systems, and protects networks from attacks.
Understand Enumeration and its role in extracting user names, machine names, network resources, shares, and services. Learn how attackers establish active connections and perform queries to gather information, identifying system vulnerabilities.
Delve into System Hacking, understanding how to compromise computer systems to access sensitive information. Learn how malicious hackers exploit system weaknesses to gain unauthorized access and take illegal advantage.
Learn about Trojans and Backdoors, understanding how attackers use Trojans to create backdoors without user knowledge. Discover how these malicious files can delete or replace critical system files, steal data, and allow remote control by attackers.
In this course, you'll explore Viruses and Worms, understanding their propagation mechanisms and how they exploit security failures to spread across networks without user action.
Learn about Social Engineering and how hackers exploit human nature to extract confidential information. Understand the tactics used to deceive users into revealing sensitive data.
Understand Session Hijacking and why attackers need session IDs to hijack sessions. Learn how session IDs are obtained and how attackers trick servers into validating their connections as legitimate user sessions.
Learn to hack web applications, detecting and preventing web attacks—a crucial skill for developers and information security professionals.
Discover how to crack wireless networks like Wi-Fi and others.
Understand Buffer Overflow, a condition where a program writes data outside its memory buffer, causing potential security vulnerabilities.
Learn about Penetration Testing (Pen Testing), the practice of testing systems, networks, or web applications to find exploitable vulnerabilities. Discover how pen testing can be automated or performed manually.
Understand Intrusion Detection Systems (IDS) and how they monitor network activities for malicious actions, generating reports for management.
Upon completing this program, you'll be equipped for roles such as:
This course spans 12 weeks, with 2 to 3 hours of daily learning, twice a week.
You're just a step away from your dream career!
Call or WhatsApp us at +1 347 219 0143 or +2349028614692.
Are you a serving corps member? Claim a 30% discount with the COUPON – DCHA-CMP1.
#professionalCourses #IctTraining #TechTalkFriday #AbujaTechCity #Microsoft #appdev
Jul 05, 2024

Jul 10, 2024

May 14, 2024


Jun 19, 2024

Oct 03, 2024

May 23, 2024
Oct 03, 2024
Jul 10, 2024


Jul 03, 2025
Apr 03, 2025